As digitisation accelerates, it’s critical for organisations to shore up their defences to ensure information systems are well protected, as Mark Venables explains.
The latest trends in cybercrime have seen it all. Advanced exploits allegedly developed by high-profile threat actors used in massive ransomware attacks, creativity of spam and phishing attacks on trending topics, and attacks relying heavily on social engineering or legitimate software used as cyberweapons. This evolution of cyberthreats calls for evolution in cybersecurity.
“The ever-changing threat landscape means every business faces unique risks and challenges, even with the most advanced anti-malware protection in place,” Russ Madley, UK head of channel at Kaspersky Lab, says. “As threats continue to grow in complexity, it’s important cybersecurity companies continue to ensure their customers are protected with the most up to date security software.”
The scale of the cybercrime threat to manufacturing cannot and should not be underestimated. In a recent survey of UK manufacturers carried out by EEF, nearly half said they have been the victim of cyber-crime, and a quarter have suffered some financial loss or disruption to business as a result.
The manufacturing sector is the third most targeted for attack, with only government systems and finance more vulnerable. Yet manufacturing – which has 2.6 million employees, provides 10 per cent of UK output and 70 per cent of business research and development – is amongst the least protected sector against cybercrime in Britain.
The report pinpointed the susceptibility of manufacturers to cyber risk, revealing that 41 per cent of companies do not believe they have access to enough information to even assess their true cyber-risk. And 45 per cent do not feel that they do not have access to the right tools for the job.
Cyber threat is holding back companies from investing in digital technologies, with a third of those surveyed nervous of digital improvement. Moreover, a worryingly large 12 per cent of manufacturers admit they have no technical or managerial processes in place to even to start assessing the real risk.
One of the easiest forms of cyberattack comes through poorly protected office systems, often the first implemented historically within manufacturing businesses. The report looks at a number of real-life examples, including two where companies production systems were infiltrated and severely disrupted after hackers gained access to their IT systems by initially hacking into unprotected office software, used to keep HR and admin records.
“More and more companies are at risk of attack and manufacturers urgently need to take steps to protect themselves against this burgeoning threat,” Stephen Phipson, CEO of EEF, says. “EEF has a vital role supporting manufacturers in the face of this challenge and we are working closely with RUSI, whose world-leading Cyber Security Research Programme is well established as a key voice to understand the fight against the threat of ever evolving cybercrime to the modern business.
“Failing to get this right could cost the UK economy billions of pounds, put thousands of jobs at risk and delay the supply of essential equipment to key public services and major national infrastructure projects. I hope this report underlines the critical risk to government and industry.”
Romaney O’Malley, head of UK regions and head of industrials at insurance company AIG Europe explains that for many manufacturers, cyber-risk is still not considered a principal risk on the risk register. Nevertheless, the cyberthreat landscape has evolved over the last year, with attacks becoming more sophisticated and more broadly disruptive.
“There is an increasing level of state-sponsored attacks between nation states, where companies infected by malware may just be collateral damage. The potential threat from cybercrime is widespread,” he says. “There is evidentially significant need for greater awareness and understanding of the importance of cyber-risk management, not only to protect existing businesses, but to create more secure environments to grow and capitalise on the potential that digital technology advances bring to manufacturers.”
Searching for the weak spot
According to ‘Paradigm Shifts’, Trend Micro’s security predictions for 2018, skills and resources are the two elements that make up an attacker’s arsenal. An attacker, however, cannot set out to break security or even perform sophisticated attacks without finding weak points in a system first. Massive malware attacks, email-borne heists, hacked devices, and disrupted services all require a vulnerability in the network, whether in the form of technology or people, to be pulled off.
It goes on to say that increased connectivity and interaction over insecure networks are a given. Unfortunately, poor implementation of technologies adds to the likelihood of threats being realised. Having protection where and when it’s needed will become the backbone of security in this ever-shifting threat landscape.
“In 2018, digital extortion will be at the core of most cybercriminals’ business model and will propel them into other schemes that will get their hands on potentially hefty payouts,” the report adds. “Vulnerabilities in IoT devices will expand the attack surface as devices get further woven into the fabric of smart environments everywhere. Business email compromise scams will ensnare more organisations to fork over their money. The age of fake news and cyberpropaganda will persist with old-style cybercriminal techniques. Machine learning and blockchain applications will pose both promises and pitfalls. Companies will face the challenge of keeping up with the directives of the General Data Protection Regulation (GDPR) in time for its enforcement. Not only will enterprises be riddled with vulnerabilities, but loopholes in internal processes will also be abused for production sabotage.”
These are the threats that Trend Micro feels will make inroads in the 2018 landscape. As such, they will serve as further proof that the days of threats being addressed with traditional security solutions are behind us. As environments become increasingly interconnected and complex, threats are redefining how companies should look at security.
Balancing risk with IOT benefits
The British media widely reported how the recent WannaCry cyberattack largely targeted NHS trusts across the country. However, what was not as widely reported was that the attack also affected many factories across the world, shutting down production and causing concerns about data security.
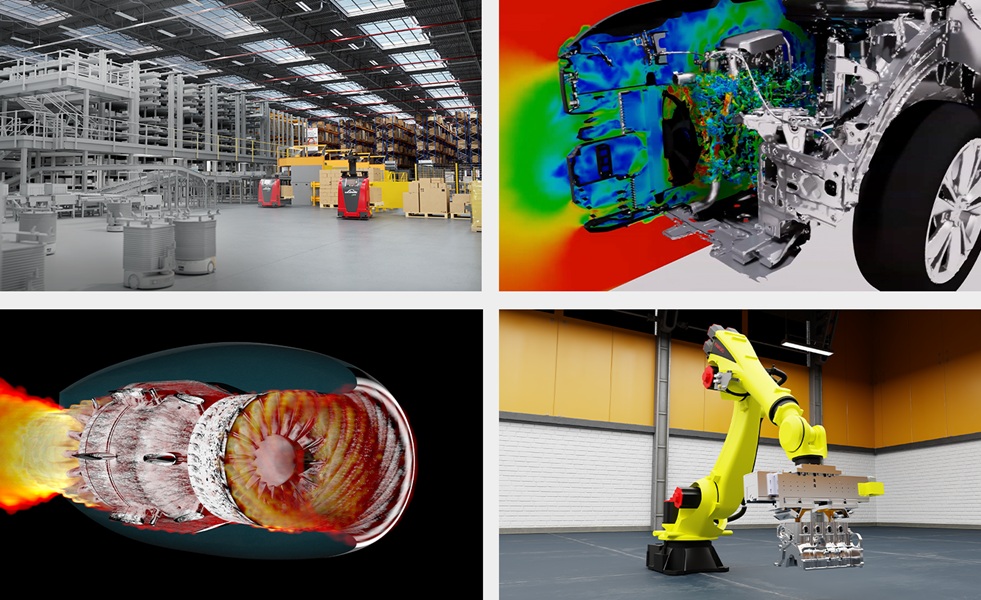
“No plant manager can deny that the internet of things (IoT) has had a substantial impact on the plant that they run,” Steve Hughes, managing director of power quality specialist REO UK, says. “They now have the ability to monitor, measure and optimise almost every process in their plant, using interconnected devices and control software such as SCADA.
“As British industries look to reverse the productivity crisis by optimising output in their factory, even small improvements in efficiency and quality can give a competitive edge.”
Although the interoperability of devices presents many benefits to the plant manager, it does present risks in terms of cybersecurity. Attackers that successfully penetrate a system can hold important and potentially sensitive data to ransom and can use the interconnectivity of devices to shut down the entire plant. “
Before plant managers introduce smart monitoring systems they should consult independent experts to perform a risk assessment and evaluate existing security measures. Plant managers should adhere to standards such as IEC 62243, which makes provisions for the network and system security for industrial-process measurement and control. This will limit the damage caused to employees, businesses and the wider industry from a potential cyberattack.
“Cyberattacks usually target conventional IT rather than operational technology (OT),” Hughes continues. “Because many monitoring systems such as SCADA are PC based, when the attack spreads throughout the network, this will affect the entire connected network of devices. Using PLCs will reduce the likelihood of this type of issue as they are not PC based. However, OT is not completely immune to the threat of cyberattacks, although these tend to be a form of industrial espionage rather than an external attack such as ransomware.
“We all know that IoT devices are good for our plants but the recent wave of cyberattacks is causing many to question their presence. However, with the right security measures in place, smart monitoring devices can play a pivotal role in the modern factory and should be embraced, rather than shunned.”
Boxout – German steel mill meltdown
While the exact details of the company involved are still unknown, the attacker used sophisticated social engineering and spear-phishing tactics to hack into the steel mill’s office computer network. Crucial controls were tampered with, making it impossible to turn off the blast furnace. The result – massive damage to the foundry.
The attacker, likely an industry insider or someone working with an insider, had specific knowledge of the production processes involved so that maximum damage could be done to the normal workings of the mill. The company’s systems were specifically vulnerable because the office network was connected to the industrial control system, meaning the attackers could effectively take control of production – and stop it from happening.
Boxout – Industrial control system attack in Saudi Arabia
In August 2017, a petrochemical manufacturer in Saudi Arabia was infected with malware that investigators believe was not simply designed to steal data or shut down operations but potentially to cause a catastrophic explosion. Significantly, it targeted operational technology in the form of industrial control systems rather than the more traditional focus on information technology.
Whilst the identity of the company affected, and the likely attackers remain unclear, it has been revealed that the target was part of the facility’s safety system, designed to stop automated equipment going beyond safe operating conditions. The malware was designed to override this.
The attack was not intercepted by the cybersecurity measures in place and failed only because as the developers of the malware had made an error in the code that caused the systems to simply shut down safely. It is likely that the perpetrators will have since fixed this error.