More than half of UK businesses have been impacted by a cyber/data security incident caused by a supply chain partner. And three-quarters of infosec professionals believe supply chain cybersecurity incidents are becoming more commonplace, according to new research published by ISMS.online.
Nearly one in three respondents cite managing vendor and third-party risk as a top information security challenge, with average fines following a data breach or violation of data protection at £237,402. The new report closely follows the warnings by the newly appointed UK Deputy Prime Minister Oliver Dowden about credible incoming attacks targeting critical national infrastructure and supply chains by unpredictable actors.
ISMS.online’s latest State of Information Security report surveyed 500 information security (infosec) professionals in the UK, comprising managers, directors, and C-level executives.
Securing supply chain data resilience
According to the survey, businesses often respond to cyber incidents by increasing information security budgets and team sizes; however, in many cases, this is too late, with businesses facing heavy financial penalties following an attack, not to mention the immeasurable reputational damage a breach can cause.
And despite 90 per cent of infosec leaders agreeing that leadership teams view strong information security as a top priority, only two-thirds (64 per cent) expect to increase their infosec budgets in the next 12 months, and just over half (54 per cent) intend to bolster their teams.
“As organisations strive to protect their most valuable information, it’s crucial to recognise that effective information security relies not only on internal efforts but also on the external partners and suppliers they work with and the effectiveness of their risk management strategies,” Luke Dash, CEO of ISMS.online, said.
“Findings from our latest report show that nearly one in three (30 per cent) cite managing vendor and third-party risk as a top information security challenge. And with the average fine nearing a potentially crippling quarter of a million pounds, it’s time business leaders take stock.
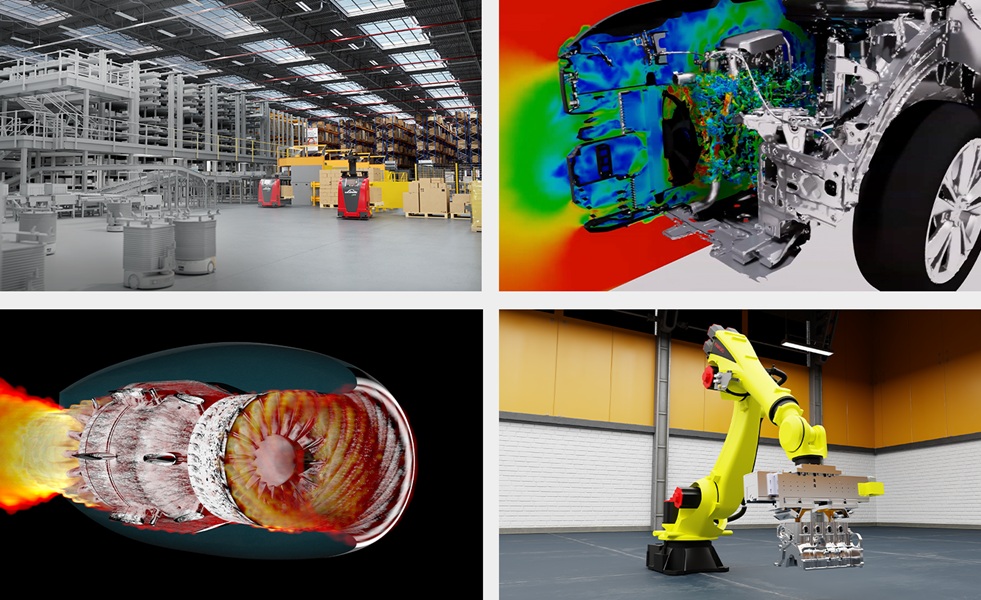
“Research from McKinsey found that on average, an auto manufacturer, for example, has around 250 tier-one suppliers, proliferating to 18,000 across the full value chain. This leaves a huge opportunity for data breaches. Investing in infosec protects information assets, builds trust, wins business, and highlights efficiencies that make a measurable difference to an organisation’s bottom line. In other words, good information security practices are good for business.”
Supply chain software is a weak link
Cyber attacks that target supply chain software are among the most destructive strategies used by cybercriminals today. Six in ten companies that have suffered a supply chain attack report significant operational disruption, data loss and reputational damage with 90 per cent of organisations taking up to a month to recover according to research by BlackBerry that found 58 per cent reported data loss, and 52 per cent reputational impact. In retail, time is money so being hit by a software supply chain attack is an expensive experience.
“These attacks wreak havoc because much of the software created and sold today is based on open source code, which can easily be compromised due to its public availability,” Keiron Holyome, VP UKI and emerging markets at BlackBerry, said.
“Vendors should, of course, check such software and research shows that IT teams believe they do; many are confident that their supply chain partners have policies in place of at least comparable strength to their own.”
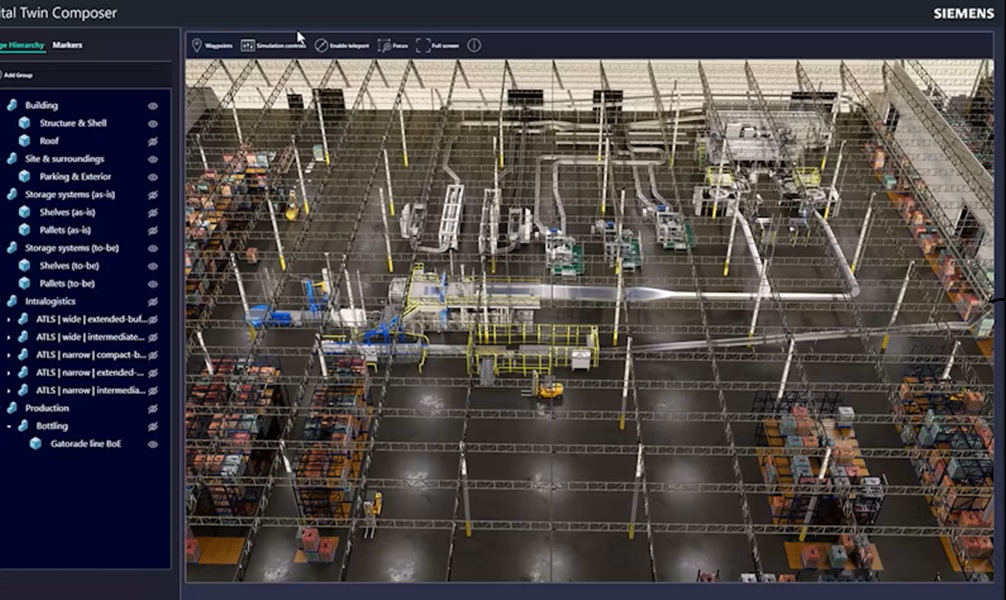
Securing a software supply chain against attacks requires knowing what elements in your system have the potential to be attacked.
More than three-quarters of those BlackBerry surveyed said that, in the last 12 months, they discovered previously unknown participants within their software supply chain — entities they had not been monitoring for adherence to critical security standards. This means that malicious lines of code can sit in blind spots for years, ready to be exploited when the attacker chooses.
The US National Cyber Security Centre recently encouraged organisations to work with suppliers to “lock shields” and boost resilience to attacks. “It’s a great initiative, but even these conversations are merely the preface to an active cybersecurity stance that helps businesses protect themselves,” Holyome adds. “No company is an island – but vigilance begins at home in preventing software supply chain attacks.”
Steps to preventing a supply chain attack
Businesses need a complete, granular view of all potential network and endpoint vulnerabilities in order to predict, prevent, discover, and respond to attacks whether direct attacks upon a business, or those coming through the software supply chain.
An extended detection and response (XDR) tool is a wise option to enable this. By collecting and analysing data from multiple sources, XDR gives the visibility and proactive action to prevent attacks that organisations need.
However, new data shows that more than three-in-four IT and cyber decision-makers currently report a lack of holistic visibility into their security posture. Change needs to take place: in the current, heightened threat landscape, a prevention-first approach to all attacks, regardless of their origin, is vital.
Across industries, companies are struggling against a cyber skills shortage. But, in the event of a cyber attack, technology like XDR – and particularly when it comes as a managed service – can significantly speed up response and remediation, meaning security teams can focus on critical roles such as activating critical event management systems and engaging with outsourced Incident Response teams if an attack strikes. Closer, quicker collaboration tends to secure a far better result.
“The threat of cyber attacks through the software supply chain remains imminent,” Holyome concludes. “As such, retail organisations must be planning their prevention and response strategies now. It’s true that businesses should put their trust in themselves to keep their software safe from hacks but there’s also no need to become overburdened. Solutions based on AI technology, backed by professional support can re-establish confidence in a secure software supply chain.”